 Recommend toStumbleUpon
Recommend toStumbleUpon
People who want to encrypt something, today, "don't know they are born"... as is true in so many fields. The computer makes very robust encryption extremely easy.
Before computers, even modest encryption was, usually, tedious or relied upon expensive machines which were only good for cryptography.
One device did exist which did create fairly robust encryption, and yet was (fairly) easy to make, and not too tedious to use.
When you know about the Vigenère cipher, you might like to look at this code wheel again, and consider the relative merits. (The Vigenère cipher was first described in 1553 (not, as so often happens, by Vigenère, but the person with priority got forgotten.) It was thought unbreakable for 3 centuries. It was "interesting" enough to catch the attention of such minds as Charles Dodgson (Lewis Carroll) and Charles Babbage... and the modest little device described here has features similar to some of the features of the Vigenère cipher.
That's one reason you should find this interesting... let's see if you do!....
Many years ago... and according to them, independently at least twice since... someone had a Neat Idea for a "machine" for encrypting text.
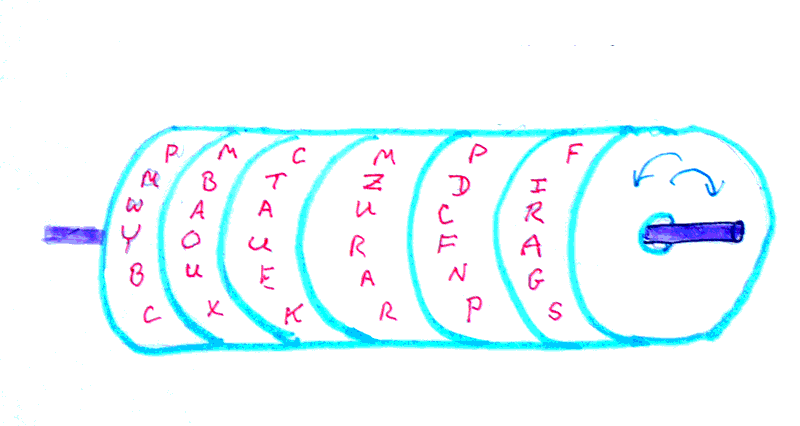
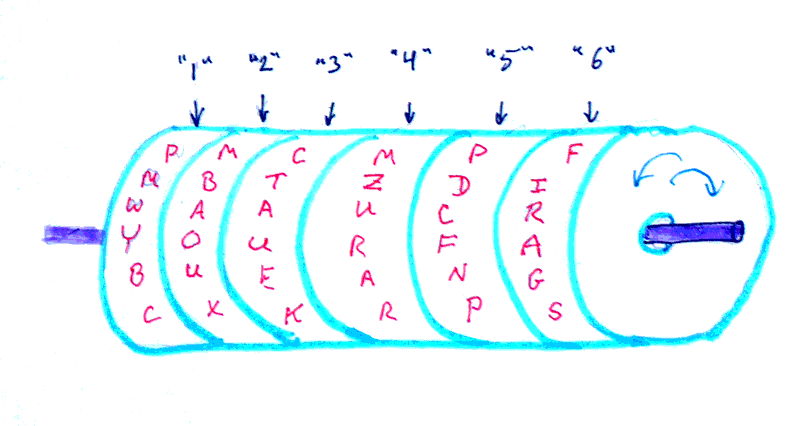
Here's a simple diagram by me of the device. (There are photos of a real one at the bottom of the page.)
That is an attempt to show six "wheels", or disks, mounted on a shaft. Each disc can be rotated on the shaft independently of the other discs. Each disc has the whole alphabet written around it, with the letters in a jumbled order. (Every letter appears at least once. If some letters appear more than once, that makes the encryption more robust, but it also makes the machine bigger.)
The person who wants to send a message has to encrypt it 6 characters at a time.
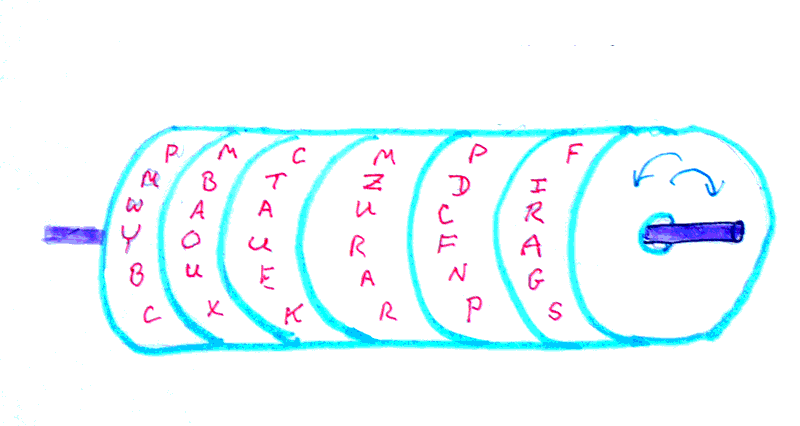
In the following, the yellow line is just "highlighting", to show you that the wheels have been rotated until the letters "YOURFA" are in a line.
The disks were rotated thus, because our hypothetical Alice is trying to encrypt "Your favor of the 22nd is received". I hope you see that the letter "YOURFA" are the first six characters of her message.
.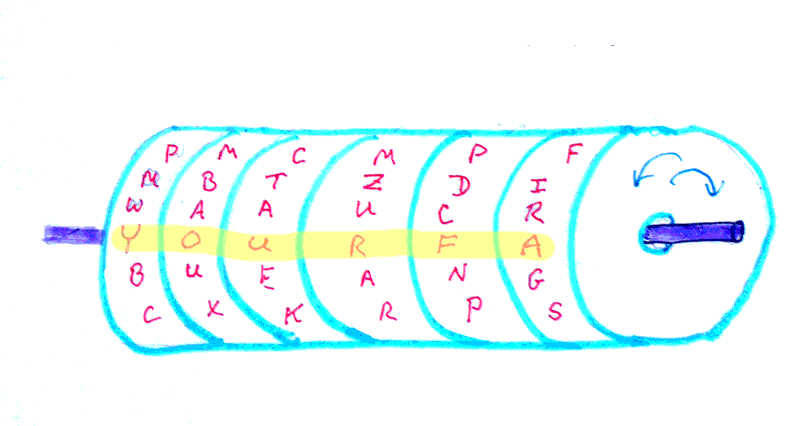
Having lined up "YOURFA", Alice then looks along any other line letters, to learn what the encrypted text is. (See next diagram....)
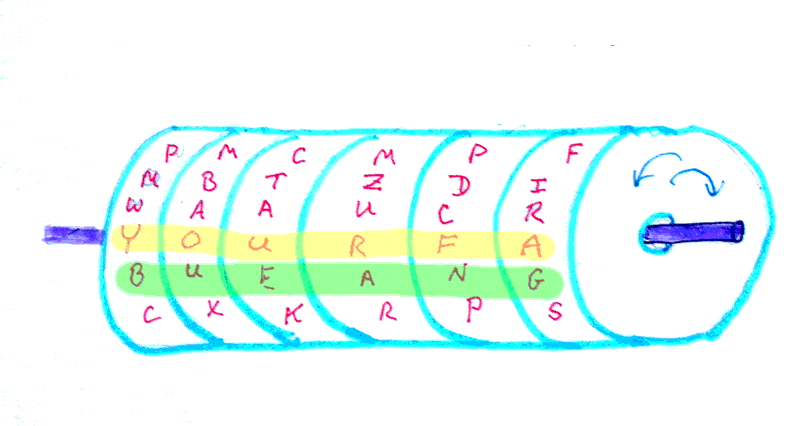
In this case, we are presuming that she chose to use the row immediately below the plaintext, which makes the ciphertext "bueang", which I hope is made clear by the green highlight line in the diagram above.
All Alice has to do is let Bob know the ciphertext, and the fact that she was using the line of letters immediately below the line with the plaintext.
(She then repeats the encryption process on the rest of the message.)
A weakness of the system, in some contexts, is that both Alice and Bob have to have a set of the disks, with the same sequence of letters on the disks. If Alice is a secret agent in a hostile environment, and the disks are discovered, it could be bad for Alice. But every system has its strengths and weaknesses.
So far, I have spoken of the apparatus as if the disks will always be on the shaft in the same sequence, but there's no reason that they must be. However, each must have an ID, and the sequence of letters around each disk must be unique, if you want to avail yourself of the advantages of not always using the disks in the same sequence.
You could add a further layer of security by adopting some system of changing the sequence of the disks on their spindle from time to time.
Even before we considered re-arranging the sequence of the discs, we could get several ciphers out of the device, by changing the row we copied the ciphertext from. (If you look back to the third diagram, you can see that the ciphertext for YOURFA could equally well have been cxkrps.)
When you add the wrinkle of rearranging the sequence of the disks, you create an extra chore for "Bob"... but also an extra barrier to people who shouldn't be reading the message. To decode a message, the recipient not only must have one of the wheel sets, but also must know the sequence of the disks on the spindle while the message was being encrypted.
Using different rows for reading off the ciphertext, and not always having the disks in the same order are examples of how the task of breaking a code can be made tedious by incorporating more than a single element into the encryption process.
Anyway, I thought that was a neat little device, and hope you did to. Another candidate for a computer simulation?
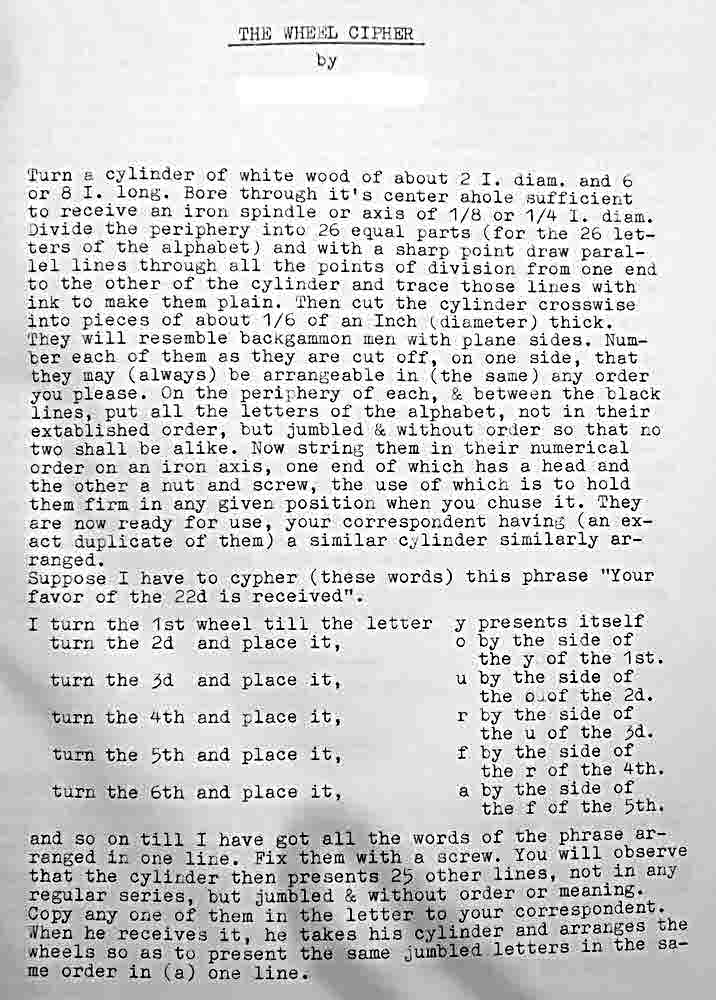
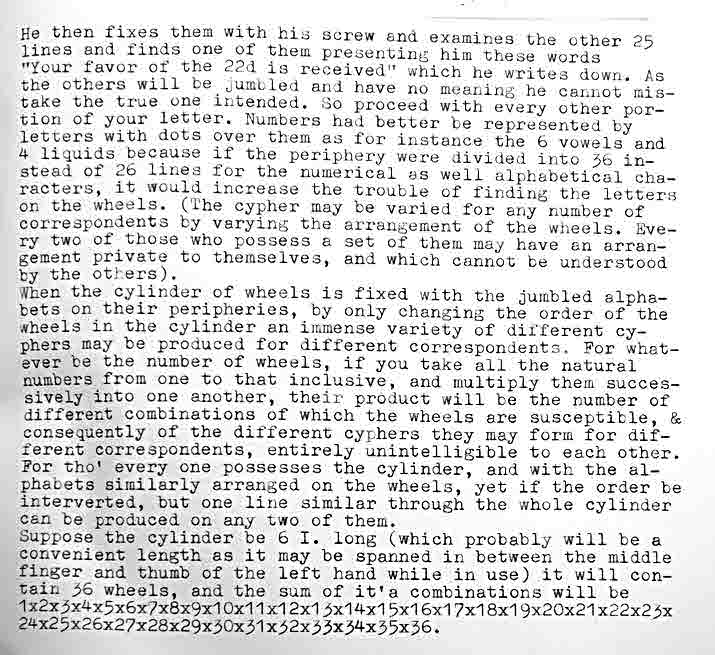
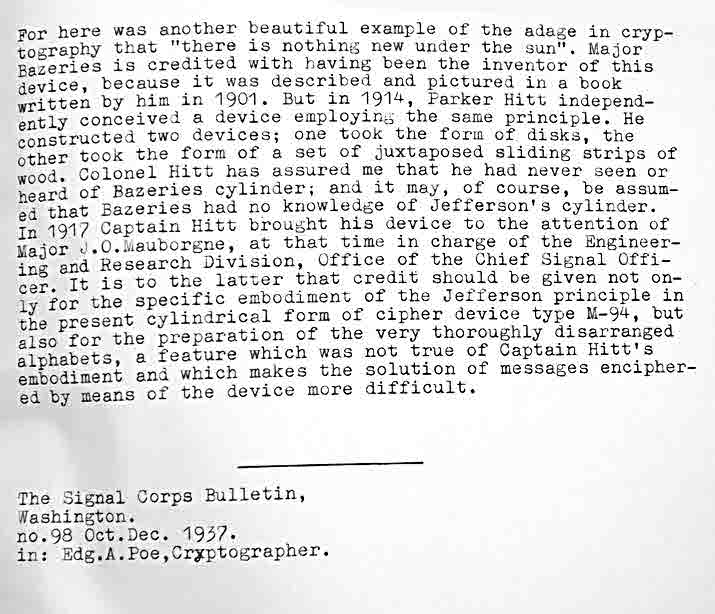
Not only is it, I think, a neat device, a neat idea, but who invented amused me. The following transcription is a description of the device by its inventor. (That text is how I first learned of it.) Have a little read. I hope you've already understood the device from what I said above. I present the transcription to give you extra data in case it helps you guess the inventor. (And in case what I said above didn't quite do the job of explaining the device.)
See what you think. (It would have been good if the original author had used a diagram or two, but in his day publishing a diagram was an expensive business, and color wasn't possible.)
Where the text says something like "2 I.", I think it means "2 inches".
So... who invented the device, do you think? (The true answer is given further down the page.)
I think you are unlikely to guess exactly who wrote this... but have a go at guessing when (roughly) and where he wrote it? I'll tell you the answer in a moment.
After the text above, in the document I was working on, there were further notes, which I also supply, further down the page. They also go into the story of others inventing the same device. For a time, the US military used a device made along the same lines.
Read no further until you have thoroughly digested the material above, attempted to guess when and where it was written.
... The answer is just a little farther down the page now...
The text was written by Thomas Jefferson (-WP-). Most citizens of the USA will know the name, I hope, and many people from elsewhere, I suspect. If you haven't heard of him, he was one of the founding fathers of the country. Here are the further notes I promised a moment ago....
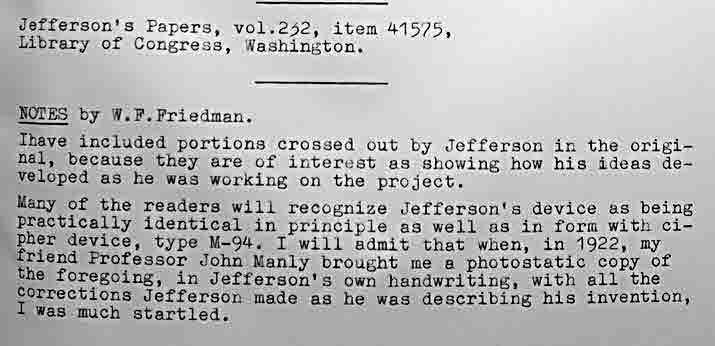
That's about it, for this page... Apart from another challenge. Did you read the introduction to these pages about cryptography and codes? If you can solve the following code, please write in, telling me what it says, and the same things I invited solvers of the other challenges to send?
Don't turn white (1/1, 1/5) with frustration, stuggling with this. I do edit this page from time to time. If you see things I should improve, please do tell me. Sorry my message is a little bizarre...
12 8 7 10 8 7 14 19 17 9 17 3 3 7 2 5 10 7 2 1 2 7 4 5
Don't expect to many hints and clues, if trying to decrypt something you aren't supposed to read in "the real world". Maybe I ramble soemtimes, but the paragraph before the coded message was not more mere rambling.
May I invite you to return to, or go to, the main Flat Earth Academy page on cryptography, ciphers and codes? If you came here by clicking on the link there, you need only close this tab or window... the main page is underneath this.
And here is a photo of a real set of wheels. This comes from my dentist's waiting room! It has been there for many years. It is set up to encrypt the classic message "Fly all is discovered", but of course, the message will have to be done six characters at a time, unless someone would care to make a few more wheels.
I've used photo manipulation to highlight the plaintext line with the two green dots. One encrypted version would be GMZABM, which comes from the line beneath, the one highlighted with yellow dots.
Have you heard of Flattr? Great new idea to make it easy for you to send small thank you$ to people who provide Good Stuff on the web. If you want to send $$erious thank yous, there are better ways, but for a small "tip" here and there, Flattr ticks a lot of boxes which no one else has found a way to do yet. Please at least check out my introduction to Flattr, if you haven't heard of it? "No obligation", as they say!
Essay on Thomas Jefferson's code wheels from Flat Earth Academy.Search across all my sites with the Google search button at the top of the page the link will take you to.
Or...
Search just this site without using forms,
Or... again to search just this site, use...
The search engine merely looks for the words you type, so....
*! Spell them properly !*
Don't bother with "How do I get rich?" That will merely return pages with "how", "do", "I", "get" and "rich".
I have other sites. My Google custom search button will include things from them....
One of my SheepdogGuides pages.
My site at Arunet.
This page's editor, Tom Boyd, will be pleased if you get in touch by email.
![]() Page tested for compliance with INDUSTRY (not MS-only) standards, using the free, publicly accessible validator at validator.w3.org. Mostly passes. There were two "unknown attributes" in Google+ button code, two further "wrong" things in the Google Translate code, and similar in Flattr code. Sigh.
Page tested for compliance with INDUSTRY (not MS-only) standards, using the free, publicly accessible validator at validator.w3.org. Mostly passes. There were two "unknown attributes" in Google+ button code, two further "wrong" things in the Google Translate code, and similar in Flattr code. Sigh.